
Cryptography is a long practised art that can be traced back to the Egyptians. Known as a way of using advanced mathematical principles to store and transfer data, the premise of crypto is one where essentially information is shared, but only those with a key can read it.
But the mathematical formulas behind that cypher or ‘secret code’ you used to play with as a child now make up some of the safest currencies in the digital world. Here’s a crash course for those interested in the cryptography behind cryptocurrencies.
The most commonly used encryption among digital assets is known as the blockchain, but when its early founders Dr. Stuart Haber and W.Scott Stornetta first proposed it in 1990, they were just trying to time-stamp a digital document.
Previously the most secure way to time and date something authentically was to mail yourself something in the post, but the discovery of cryptographic hash functions was to change all that. Haber and Stornetta proposed that if you took the input of a document and distilled it into a fixed-size alphanumeric string, then that string could essentially be the documents digital fingerprint (or hash value). Essentially it would tell you when the document existed in time and how big it was, but not the contents.
By entering this hash value into a chronological order of other documents it would create a block like form, separated only by other blocks further up or down the order. Drawn on a blackboard, it was easy to link these blocks via a chalk string or chain, and so the block chain was born (although not later named as such until after Satoshi’s Bitcoin white paper).
There are cryptocurrencies based on other mathematical functions though, such as IOTA, which asks the user to verify two randomly selected previous transactions before completion, each of which refer to two other transactions. This “tangled web of confirmation” is certainly cheaper than blockchain but the mathematical formula has already come under scrutiny and needed one patch.
When it comes to security, you might hear the terms salting, sharding and Password Based Key Derivation Functions (PBKDF1 and PBKDF2 for short).
These are industry standards that attempt to keep safe your information. Let’s start with a salt, this is a completely random string of text added to even the most common passwords that makes it harder for any would-be hackers. Whether you use the same or different passwords for multiple logins, each is given a different randomly generated salt which is distilled down into a cryptographic hash function.
To do this you need to concatenate them, i.e. the Hash value becomes salt plus password. Now a common password such as password1 instead becomes 9$dK!3gCAJ£password1. Far more secure and you won’t ever need to remember it. The beauty is that with modern technology, your computer probably already produces these salts.
A step further is PBKDF2 which takes an input of a passphrase along with a salt value and repeats it to form a derived key. When the standard was written in 2000, it was suggested that the minimum number of iterations stood at 1,000 but that has since been increased significantly to compensate for CPU speeds. This reduces the chance of hacking as multiple passwords will all have to be tested individually.
Finally, when it comes to blockchain, a database technique known as sharding has become popular. It involves separating the nodes and sharing them between other compatible servers, maintaining the decentralization. But the technique involves adding a proof of stake (PoS) consensus algorithm, which involves designated nodes that take transaction validation responsibility. Once successfully validated, the nodes (or ‘stakers’) earn whole or part of the transaction fee but you will need to build up your credentials or ‘validations’ to be entitled to handle more transactions.
Mathematics don’t just play a part in the encryption and security of a cryptocurrency, they also make up part of the digital standards, such as PGP.
PGP – or pretty good privacy – was created in 1991 to provide digital privacy and authentication using accessible cryptographic methods. It includes a combination of hashing, data compression, symmetric-key cryptography and public-key cryptography to provide both a private and public key facility.
OpenPGP takes this one step further. For instance, web based applications can now use PGP encryption web browsers while iOS and Android now offer several OpenPGP compliant applications.
The November 2007 specification RFC 4880 specified a suite of required algorithms to ensure encryption and signing and has since been extended to support the Camellia cipher (2009) further signing and key exchanges (2012) and finally ECC encryption (2014).
Due to its continued refinement, there are some crossovers between old and new PGP, so it’s worth checking what standards your communications fall under.
As cryptocurrency evolves, so does the potential for discrepancies. From collisions, where two hash keys have the same value, to Trojan horses forcing computers to mine for them, the threats are real. But with so much cryptographic effort now involved, the solution is often provided long before the problem occurs.
Even Haber and Stornetta weren’t correct in their first digital time stamping paper, it took another for them to rectify the previous solution to collisions, and that continues in all forms of cryptography.
It’s why we’re working in PBKDF2 instead of PBKDF1, and why SHa3, the latest secure hash standard, was produced by a competition winner in 2012 before rolling out in 2015.
But if you are still using plain text, from emails to more sensitive information, be wary of sniffers. A sniffer is a piece of software that grabs all of the traffic flowing into and out of a computer attached to a network.
Here, anything submitted in plain text can be accessed, and as the sniffer can be customised you will never know how much damage has been done, as it leaves no damage to a network environment. So whether you use an anti-sniffer or encryption, the mathematics within cryptography are still keeping our information safe some 5000 years since the Egyptians first discovered them.
At Copper, we use a combination of encryption methods for the destruction of private keys, the creation of distributed keys, and the co-signing required for digital asset withdrawals. We also have the added protection offered by operating in a server-less environment, negating the threat from sniffers. To learn more you can read about the Copper Unlimited storage solution, or get in touch.
Insights

Market Insights
23.01.2024
Coppercasts
24.07.2024
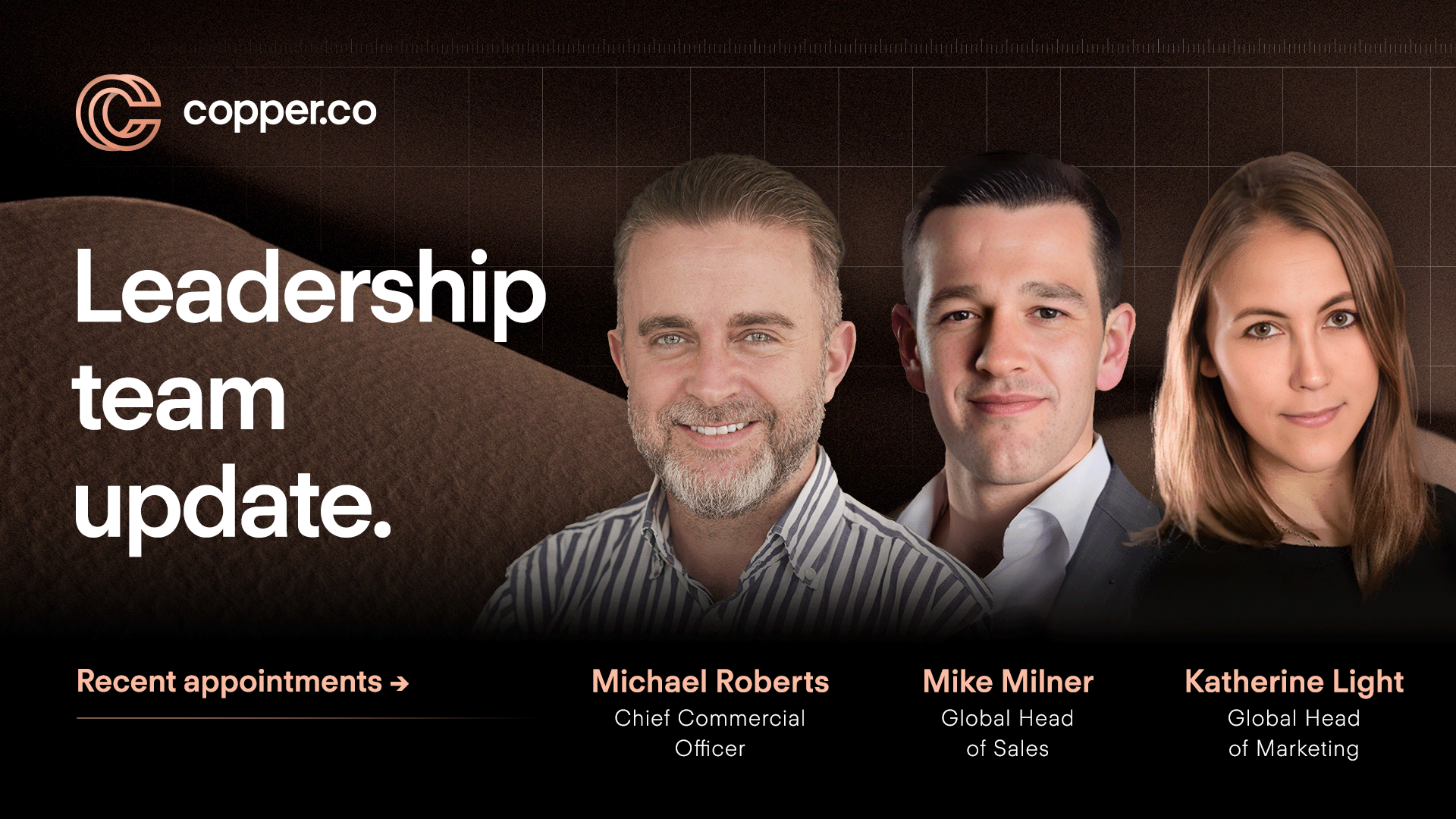
Company News
23.07.2024